Classification: TOP SECRET – EYES ONLY
Phase Two Codename: IRON VEIL
1. Phase Two Objective
SABLE’s handoff of a key indicates the existence of a secure location — likely a storage unit, safe deposit box, or covert cache. Phase Two focuses on:
- Identifying the lock the key belongs to
- Determining the purpose of the cache
- Mapping SABLE’s network
- Maintaining full deniability and zero detection
This phase is active intelligence gathering, not confrontation.
2. Updated Threat Assessment
SABLE’s behaviour suggests:
- He is operating alone
- He is following a pre‑planned sequence
- He is avoiding digital communication entirely
- He is preparing for a retrieval or a reveal
MI5 analysts believe the cache may contain:
- Old intelligence files
- A contingency asset (documents, currency, or tech)
- Evidence of a dormant network
- A message intended for a third party
3. Phase Two Team Assignments
| Unit | Codename | Phase Two Role |
|---|---|---|
| Technical Intelligence | LANTERN | Key‑matching, CCTV triangulation, digital forensics |
| Field Surveillance | HARRIER | Shadow SABLE’s movements to identify the cache location |
| Mobile Team | GHOSTPACK | Rapid redeployment and silent perimeter coverage |
| Covert Entry Specialists | LOCKSTEP | Non-destructive access to the cache once located |
| Analyst Cell | QUILL | Predictive modelling of SABLE’s next moves |
4. Key Analysis Protocol
LANTERN initiates Operation KEYMATCH, a three‑step process:
Step 1 — Physical Characteristics
- Brass alloy
- Standard British cut pattern
- Slight wear on the shoulder
- No manufacturer stamp
Step 2 — Likely Lock Types
- Self‑storage units (older facilities)
- Safety deposit boxes (pre‑2000 models)
- Abandoned commercial properties
- Railway station lockers (legacy units still in service)
Step 3 — Geographic Probability
Cross‑referencing SABLE’s known travel corridor:
Code
Heathrow → Piccadilly Line → Westminster → Southbank
QUILL identifies 14 possible lock sites within a 2.5 km radius of Southbank.
5. Phase Two Operational Map (Text-Based)
Code
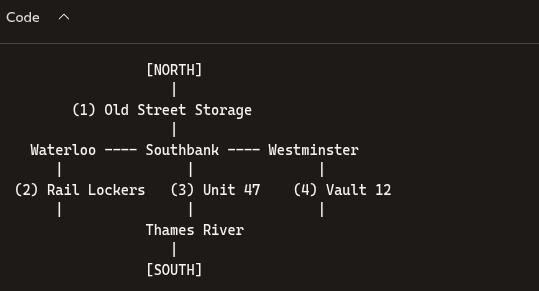
Priority Sites:
- Southbank Unit 47 — abandoned since 2011
- Waterloo Rail Lockers — legacy units still active
- Vault 12 — private deposit facility with minimal oversight
6. Phase Two Action Plan
A. Track SABLE’s Next Move
HARRIER shadows SABLE at a distance of 40–60 metres. GHOSTPACK rotates vehicles to avoid pattern detection.
B. Identify the Cache
LANTERN monitors CCTV for key‑in‑lock behaviour. QUILL predicts the most likely time window for retrieval.
C. Covert Entry
LOCKSTEP enters the cache after SABLE departs. Rules of engagement:
- No trace of entry
- No disturbance of contents
- Photograph, document, extract intel only
D. Shadow Network Mapping
If SABLE meets additional contacts:
- No engagement
- Identify
- Tag via remote observation
- Add to network map
7. Contingency Protocols
If SABLE detects surveillance
- Immediate disengagement
- Switch to long‑range tracking
- Deploy decoy civilian movement patterns
If the cache contains hazardous material
- LOCKSTEP withdraws
- HAZMAT team (codename FALCON) deployed
- Area quietly cordoned off under a civilian pretext
If SABLE attempts to flee London
- GHOSTPACK intercepts routes
- Passive tracking only
- No confrontation unless authorised by OVERWATCH
8. Phase Two Narrative Scene (Fictional)
Location: MI5 Mobile Command Unit, parked near Waterloo Time: 02:15
Rain taps against the roof as the monitors flicker with CCTV feeds. HARRIER leans over LANTERN’s shoulder.
LANTERN: “Got him. Camera 12. Southbank underpass. He’s holding the key.”
The room tightens. OVERWATCH’s voice comes through the encrypted channel, calm but razor‑sharp.
OVERWATCH: “Teams, this is Phase Two. Maintain distance. Do not lose him.”
On the screen, SABLE pauses at a rusted metal door marked 47.
QUILL: “That’s our cache.”
OVERWATCH: “LOCKSTEP, stand by. Entry only after SABLE clears the area.”
The team watches as SABLE unlocks the door, slips inside, and emerges three minutes later carrying nothing.
HARRIER: “He left something behind.”
OVERWATCH: “Then retrieve it. Quietly.”
The operation moves into its most delicate moment.


Leave a comment